In this post, I am gonna teach you how you can have a secure server using Cloudways.
Cloudways is a panel that you can use to manage a server or multiple server to host your WordPress sites and other type of web applications.
I used mainly for WordPress and I don’t want to my sites to be part of the thousand of sites that are hacked every day
I moved to Cloudways from WordPress.com more than three years ago and I have learned so many things to secure my server or sites and I would like to share them so you don’t have to worry about hackers that much and focus on what really matters
Hide your Server IP with CloudFlare
I recommend CloudFlare to protect your server and WordPress sites.
When you add your domain to CloudFlare, CloudFlare will hide the IP so attackers have a hard time finding it.
If you don’t want people on the internet know what your hosting provider is, CloudFlare will take care of that automatically for you.
This is what you see when you try to know who my hosting provider is and what my server IP address is.
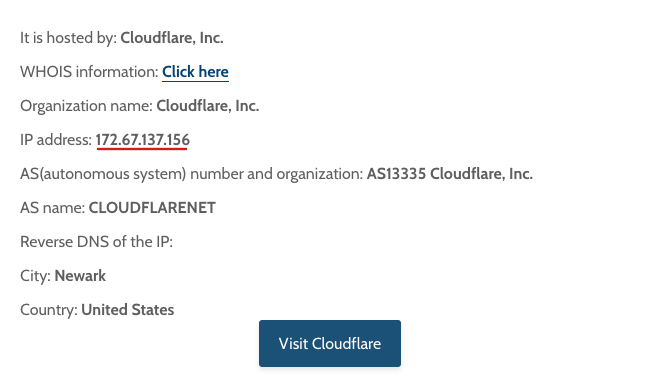
I am sure there are workaround to find your server IP address and where your sites are hosted but the point is making everything harder for hackers.
Use CloudFlare Firewall Rules
If you are active person in WordPress, you will see people asking what the best security plugins are.
WordFence, Sucuri and Solid Security are some of the most popular options.
I don’t recommend any security plugins because I protect my sites using custom CloudFlare Firewall rules.
If you have content sites, which are pretty much static sites, you can harden your website by blocking all access to files which might lead to your sites getting hacked.
Limit Database, SFTP and SSH Access to IP Addresses you Trust
You probably don’t check any of this often but it is a measure that you can apply to protect your database, WordPress Core Files and SSH access.
You can do this by simply by choosing “Block all IP addresses, except those on the Whitelist.”
Then add your IP or don’t add any IP address unless you or your developers need access to the database, WordPress installation, etc.
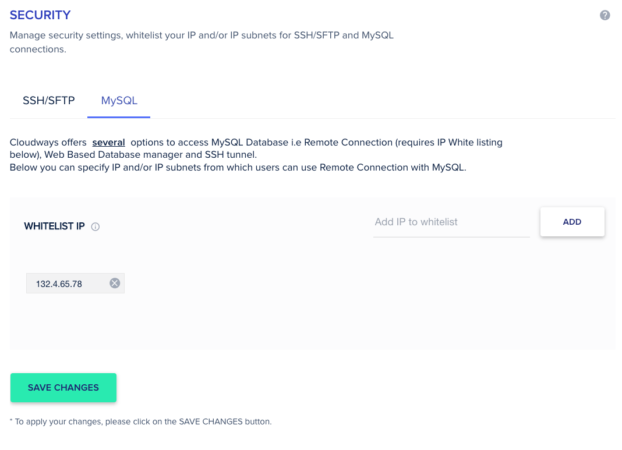
If I get a hold of your database, SSH or SFTP credentials, I won’t be able to connect to them unless my IP has been previously whitelisted.
Make Backups
Backups on Cloudways are pretty affordable with Cloudways, so make them regularly so you can revert back to a previous state if your sites gets hacked or defaced.
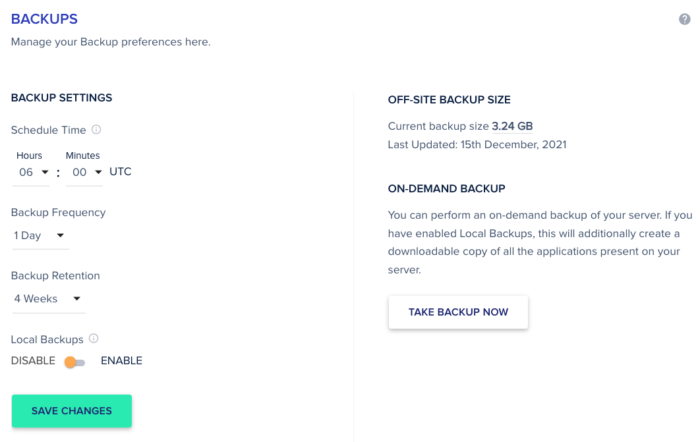
Also consider making backups that you can save on a cloud service like Dropbox, Box, Drive etc.
I create backups using All in One WP Migration and store them on my Google Drive
Off-site backups are useful if your server is down and you want to restore your site in a different server.
Disable Access Application via IP
Another security measure that you can take by simply disabling access to your application via IP
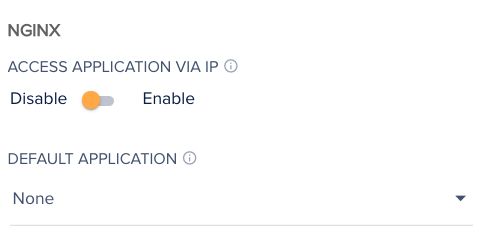
In default application, choose none.
This is what people on the internet will see when they try to access your sites via the server IP
Update Plugins and Themes Regularly
Another piece of advice for your site not to get compromised is to update your plugins, themes and WordPress Core Files regularly.
I usually update WordPress, my theme or plugins as soon as an update has been released
I understand why some people take some time to make sure there are not major issues related with WordPress core, theme or plugin update.
If your part of that group, make sure you check first if the update has to do with security fixes or not.
Choose the best theme and plugins so you don’t have to worry that much about security issues or site breaking.
What about Bot Protection?
Bot Protection is basically Malcare, another security plugin out there.
I don’t use it. I think it is a good alternative in case you don’t want to use CloudFlare
If you have CloudFlare Firewall rules, CloudFlare is far more powerful than Bot Protection.
What about the Vulnerability Scanner?
The vulnerability scanner is powered by Patchstack
If you have lots of sites and you don’t want to log in to each of them to see if everything is properly updates, you can check the status of your WordPress core, themes and plugins from your dashboard.
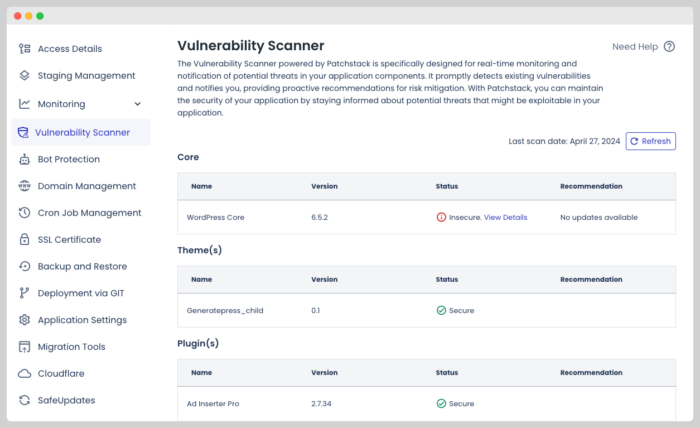
I usually install four to five plugins in each one of my website so I am not really concerned about the state of those plugins.
If the WordPress core, your theme or your plugins has a major security issues, you will get an email to let you know the risk your WordPress site is taking by not updating promptly.
Take WordPress Security Seriously
At this point, everything is pretty much taken care of, CloudFlare Firewall Rules will handle most of the malicious activity if the rules are successfully implemented
Don’t make stupid mistakes like using nulled plugins or using your dog’s name as password.
Use BitWarden to create and save 30-character passwords for your sites and web services used to manage your sites.
Don’t click on any suspicious links or visit shady websites cause you don’t want to pay for an UFC event or movie.

If you write posts on public places, create an editor account for such purposes and use your admin account only when you really need to.
Conclusion
Cloudways has proven to be one of the best ways to create and protect your server.
I haven’t had any issues and when I have run into some problems was because I didn’t follow the recommendations included in this post.


